Your partner in designing, implementing and continuously strengthening your identity security landscape.
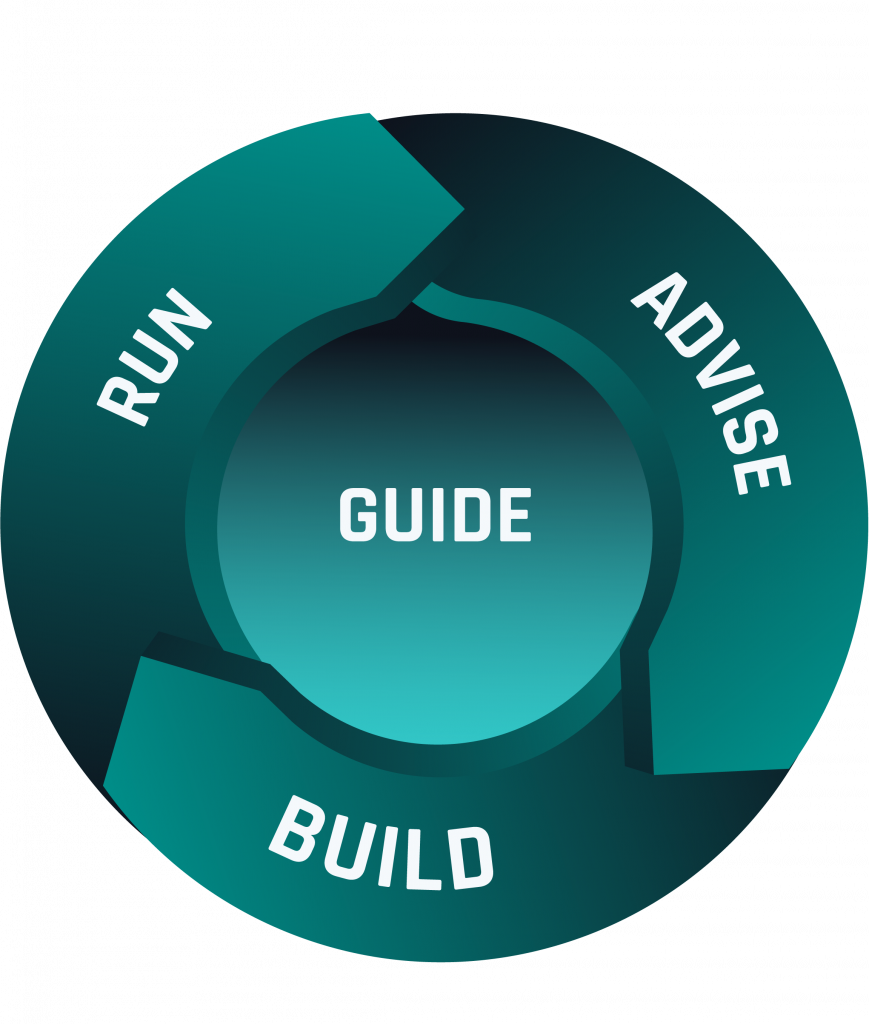
Identity Security is not a one-time project.
It’s a continuous process that requires ownership and direction.
Independent, honest and business-oriented.
Vendor-agnostic where required, pragmatic where possible.
We translate best practices into realistic roadmaps tailored to each organisation’s maturity and sector context.
Implementation of proven technologies, measured by sustained control, not by go-live.
No generic templates, solutions aligned with organisational reality.
Operational support when required, ensuring stability and performance, including extended service windows.
Continuous guidance and ownership beyond implementation.
We stay involved to optimise, adapt and strengthen Identity Security as risks and business needs evolve.
At IdentIT, we act as an Identity Security Partner with a focus on three critical domains:
Our core expertise for more than 10 years.
Designing and implementing secure authentication, authorisation and access control architectures (forming the technical backbone of digital trust).
Establishing lifecycle management, role models, compliance frameworks and access reviews, ensuring organisations regain structural control.
Providing insight into access risks and identity exposure, enabling organisations to understand their current state and take informed next steps.
Unlocked is our recurring series where we take on the most common, and most critical, questions in the field of Identity Security. Each session brings you concise insights, practical demos, and expert conversations to help you navigate your digital identity challenges with confidence.
We sat down with Elimity to explore the emergence of Identity Visibility and Intelligence Platforms (IVIP).
While many large organizations still struggle to answer ‘Who actually has access to what?’, IVIP addresses the critical visibility gaps that traditional IGA and PAM tools often miss. We discuss how this Gartner-defined category replaces orphaned accounts and fragmented data silos with a single pane of glass, helping you shrink your attack surface and streamline compliance.
Discover how businesses are transforming their identity security strategies with our solutions. From boosting efficiency to enhancing security, these success stories showcase real results.
We integrate trusted platforms to ensure secure, seamless access and compliance, empowering businesses to protect user identities across all digital touchpoints.






Don’t hesitate to reach out if you need more information.