Managing customer identities and access has become a top priority for organizations in a world where data privacy and security are paramount. The days of scattered and disparate identity management systems are long gone. Now, the strategic imperative is clear: centralize the management of customer identities and access to stay ahead in the game.
Game-Changing Benefits of Centralized Management
In this article, we’ll explore how centralizing the management of customer identities and access can revolutionize the way organizations operate, securing sensitive information and simplifying complex processes. We will help you grasp the true game-changing potential of this approach.
Understanding the Challenges
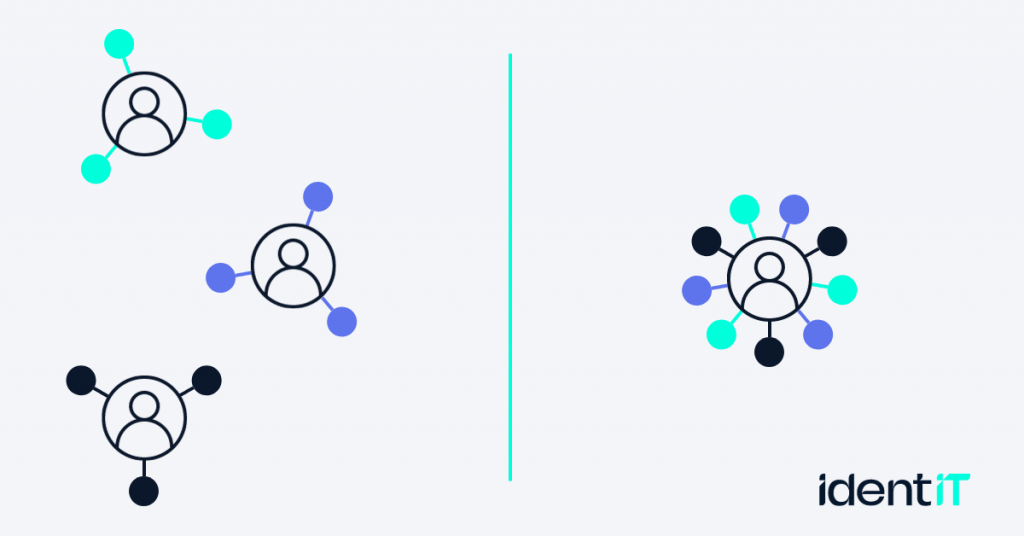
To understand the need for centralized management, it’s crucial to acknowledge the challenges organizations face in managing customer identities and access.
Challenges in Managing Customer Identities and Access
- Fragmented Data: In decentralized systems, customer data is often scattered across multiple platforms, making it challenging to gain a holistic view of each individual. This fragmentation can lead to inefficiencies and missed opportunities for personalization.
- Inconsistent User Experience: Decentralized access and identity management can lead to inconsistencies in the user experience. Users may need to log in multiple times or encounter different authentication methods, resulting in frustration and potential drop-offs.
- Inefficient Access Control: Decentralized systems can result in inefficiencies in granting and revoking access. It becomes challenging to manage permissions, potentially leaving security vulnerabilities unaddressed.
The Complexity Conundrum
Centralized customer identity and access management can alleviate some of these challenges by streamlining processes and data. However, it’s essential to have a look at the multifaceted nature of complexity in decentralized approaches:
- Interconnected Systems: In a decentralized setup, various systems might be involved, each with its authentication methods and data structures. Integrating and maintaining these connections can be labor-intensive and error-prone.
- Security Risks: Decentralized systems can open doors to security vulnerabilities, as managing security consistently across multiple platforms can be challenging. This increases the risk of data breaches, unauthorized access, and compliance violations.
- Operational Inefficiencies: The need to maintain multiple systems, each with its set of protocols and procedures, can lead to operational inefficiencies. It may result in higher costs, slower response times, and an increased administrative burden.
The Power of CIAM
In the digital realm, where the proliferation of online services and platforms is overwhelming, there’s a dire need for a comprehensive solution that can effectively manage customer identities and access. This is where Customer Identity and Access Management (CIAM) steps in, promising a streamlined, secure, and user-centric approach.
Centralizing Identity and Access Management
One of the remarkable attributes of CIAM is its capacity to centralize identity and access management, addressing the challenges associated with decentralization. Here’s how it accomplishes this feat:
- Unified User Database: CIAM consolidates user data into a single, unified database, allowing organizations to maintain a comprehensive view of customer identities. This centralization reduces data fragmentation and simplifies the management of customer information.
- Standardized Authentication: CIAM provides a standardized authentication process, ensuring that customers have a consistent login experience across all services. This eliminates the inconsistencies that often plague decentralized approaches.
- Efficient Access Control: With CIAM, access control becomes more efficient. Administrators can easily set, modify, and revoke permissions from a centralized dashboard, reducing the risk of unauthorized access and data breaches.
Benefits of Centralized Management
In our exploration of centralized management, we’ve reached the stage where we unveil the compelling benefits it brings to the table. Let’s dive into two key areas where centralized management truly shines: security and simplicity.
Improved Security
Data breaches and cyber threats loom ominously, and security is a non-negotiable priority for any organization. Centralized management, through the implementation of CIAM, offers a robust solution:
- Streamlined Security Protocols: By centralizing access controls and authentication processes, CIAM ensures that security protocols are consistent and standardized. This uniformity reduces the likelihood of vulnerabilities slipping through the cracks.
- Enhanced Authentication: CIAM incorporates advanced authentication methods, such as multi-factor authentication and biometrics. These measures significantly bolster the protection of customer identities and access.
- Real-time Monitoring: Centralized management allows for real-time monitoring and threat detection. Any unusual or unauthorized activities are promptly identified and addressed, minimizing the risk of data breaches.
Reduced Complexity
The complexity of decentralized identity and access management is a thorn in the side of many organizations. CIAM steps in as a breath of fresh air, simplifying this complexity in several ways:
- Single Sign-On (SSO): CIAM’s SSO functionality eliminates the need for users to remember multiple login credentials. This not only simplifies their experience but also reduces the burden on help desks dealing with password resets.
- Efficiency Gains: Centralized management enhances efficiency by providing a unified platform for identity and access control. This streamlines administrative tasks, saving valuable time and resources.
- Cost Savings: A more efficient and secure system directly translates into cost savings. Fewer security incidents and a reduction in administrative overhead contribute to a healthier bottom line.
Positive Impact on the Customer Experience
Centralized management, primarily through CIAM, holds the key to a positive and seamless customer experience:
- Convenience: Customers value convenience above all else. With CIAM’s single sign-on, they can access various services with a single set of login credentials. This eliminates the hassle of remembering multiple passwords and streamlines their interaction with your brand.
- Personalization: CIAM enables organizations to gather and utilize customer data effectively. This data can be harnessed to personalize user experiences, tailoring offerings, recommendations, and interactions to individual preferences. Customers feel valued and understood, fostering a sense of loyalty.
- Trust and Transparency: CIAM ensures that customers have control over their data. They can grant or revoke consent, and their information is protected. This transparency and respect for their privacy build trust, an invaluable asset in today’s business landscape.
Centralized management, as exemplified by CIAM, is more than just an operational efficiency booster; it’s a potent tool for creating a customer-centric, personalized, and trustworthy environment that nurtures customer loyalty and drives success. In the following sections, we’ll explore real-world examples of how
Conclusion
In conclusion, centralized management of customer identities and access, facilitated by Customer Identity and Access Management (CIAM), emerges as a transformative force in the modern digital landscape. By addressing the challenges of fragmented data, inconsistent user experiences, and inefficient access control, CIAM streamlines operations, enhances security, and simplifies and enhances the customer experience.
As organizations increasingly recognize the compelling benefits of centralized management, it’s clear that CIAM is not just a game-changer; it’s a strategic imperative for those seeking to excel. It offers a pathway to operational excellence, heightened security, and a customer-centric approach that builds loyalty and drives success.
